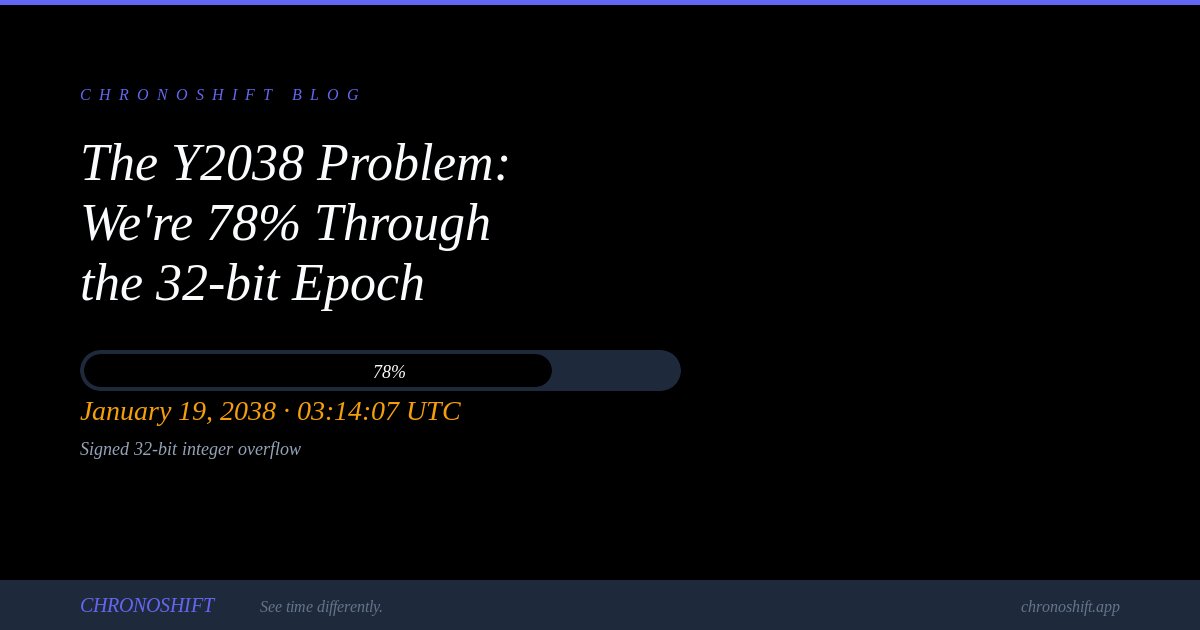
The Y2038 Problem: We're 78% Through the 32-bit Epoch (Live Counter)
On January 19, 2038, at exactly 03:14:07 UTC, the number of seconds since the Unix epoch will hit 2,147,483,647 — the maximum value that fits in a signed 32-bit integer. One second later, systems still using 32-bit time will overflow, potentially wrapping to a negative number that represents December 13, 1901.
See the live Y2038 countdownWe are currently about 78% of the way through the signed 32-bit epoch range. The clock is ticking.
The Math Behind the Problem
A signed 32-bit integer can represent values from -2,147,483,648 to 2,147,483,647. Unix time started counting from 0 at midnight on January 1, 1970. At one second per tick, it takes exactly 2,147,483,647 seconds — about 68 years — to reach the maximum. 1970 + 68 = 2038.
When the counter hits 2,147,483,647 and increments by 1, the bit pattern wraps around. In two's complement representation (how computers store signed integers), this flips to -2,147,483,648 — which Unix systems interpret as December 13, 1901. Time effectively jumps backward by 136 years.
What Systems Are Actually at Risk
The good news: most modern systems have already migrated to 64-bit time representations. A signed 64-bit timestamp won't overflow for about 292 billion years. The bad news: plenty of systems haven't migrated.
- Embedded systems and IoT devices with hardcoded 32-bit time (industrial controllers, medical devices, automotive systems)
- Legacy databases with 32-bit TIMESTAMP columns (older MySQL versions default to this)
- Firmware in devices with 20+ year expected lifespans deployed before the fix was common
- File systems: ext3 timestamps are 32-bit signed (ext4 added nanosecond precision with larger fields)
- Old C/C++ code using time_t on 32-bit compilers without the _TIME_BITS=64 flag
- Network protocols and file formats with fixed 32-bit time fields baked into their specifications
- GPS systems (GPS time is separate from Unix time but some receivers use 32-bit Unix conversion)
What the Industry Has Done
Linux kernel: Since kernel 5.6 (2020), all internal time representations are 64-bit, even on 32-bit architectures. The kernel can now represent dates until the year 292,277,026,596. User-space applications still need to be compiled with 64-bit time support.
glibc: Since version 2.34, glibc on 32-bit Linux uses 64-bit time_t by default when compiled with _TIME_BITS=64. Distributions like Debian and Ubuntu have been rolling this out.
Databases: MySQL 8.0+ uses DATETIME instead of TIMESTAMP for new tables by default, avoiding the 32-bit limit. PostgreSQL has always used 64-bit timestamps internally.
Apple: macOS and iOS have used 64-bit time since the transition to Intel (2006) and ARM64 (2013) respectively.
Windows: FILETIME has always been 64-bit (counting from 1601), so Windows itself is not directly affected, though Windows applications using Unix time may be.
Testing Your Systems Now
You can test for Y2038 vulnerability by setting test system clocks to January 19, 2038 and observing behavior. Many organizations are beginning this testing as the date approaches. Key things to watch for: date displays showing 1901 or 1970, certificate validation failures, cron jobs misfiring, and database query errors on date ranges that span 2038.
Check if your timestamps are Y2038-safeThe Countdown Continues
With roughly 12 years remaining, the Y2038 problem is no longer a distant hypothetical. Systems being deployed today with 20-year lifespans will still be running when the clock rolls over. If you maintain any system with 32-bit time dependencies, now is the time to audit and migrate.